Audit Logs
Enterprise organizations have access to audit logs, detailing the creation, modification and deletion of Losant resources by your organization's team members. This allows administrators to view a trail of edits made to any resource owned by that organization.
If audit logs are enabled for your organization, and you have administrator permissions for the organization, you will find a link to the logs in the of the "Settings" tab:
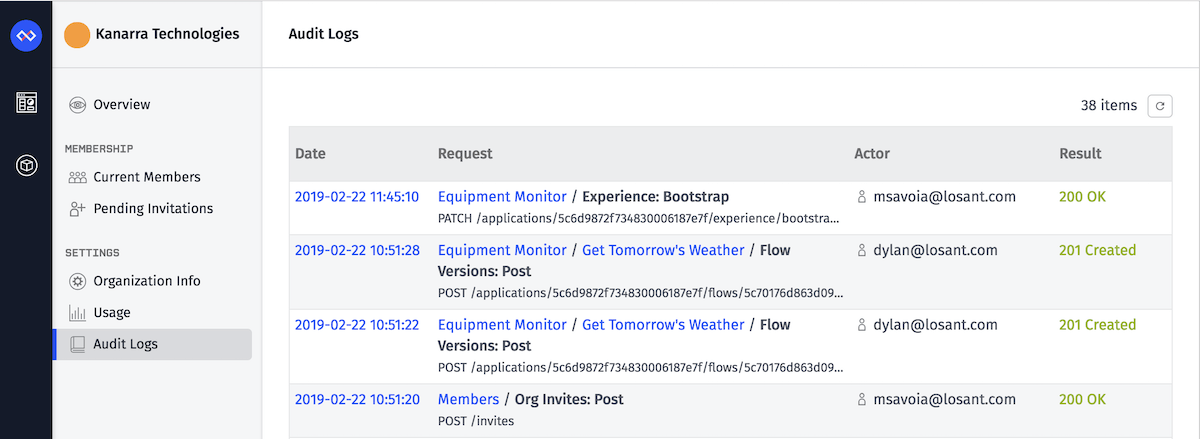
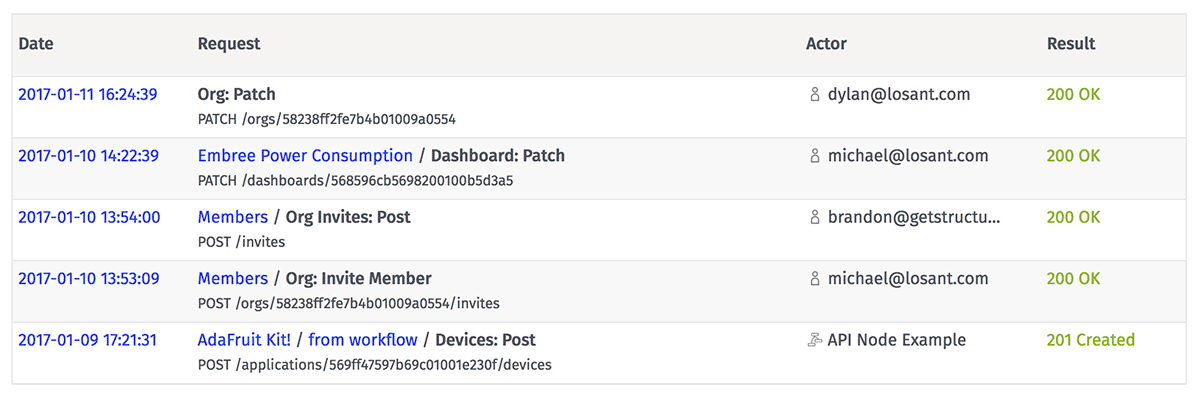
Log Entries
Currently, log entries are sorted by timestamp (latest to earliest). Audit logs are available for all organization edits from the second week of January 2017 onwards, and the records are kept for one year regardless of your organization's data retention plan.
Available Information
The following information is available for each request included in the audit log:
- Request ID
- Timestamp of request
- URL path and HTTP method, which maps to a Losant API method
- Query parameters included in the request, if applicable
- Request body, if applicable
- Request initiator (usually an organization member, but occasionally a workflow or other entity)
- Response body, if applicable
- HTTP response code
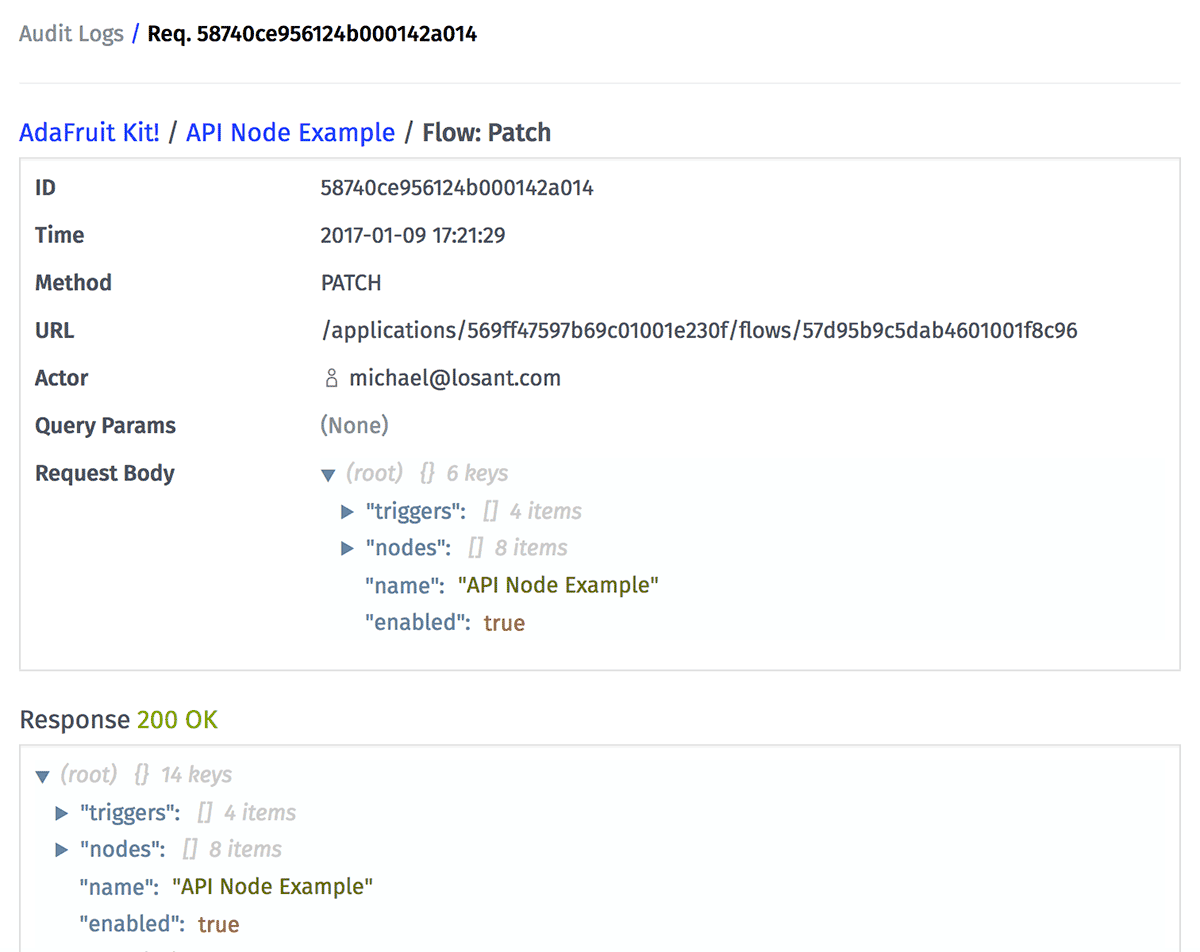
Note that a number of sensitive details, such as application key secrets, credit card numbers and invitation tokens, are redacted from the audit logs for security purposes.
What's Recorded
As a general rule, any request that creates, edits or deletes a Losant resource will appear in the audit logs. More specifically ...
- Edits to the organization itself, such as name or description changes
- Changes to organization members, such as leaving the organization or changing a member's role
- Creation, revocation, acceptance or deletion of any member invitation
- Transfer of resources to or from the organization, whether the other party is another organization or a user's Sandbox
- Creation or deletion of any application or dashboard owned by the organization, or edits to those resources. This includes application sub-resources, such as:
What's Not Recorded
Not everything that happens within your organization is available in the audit log. Here are a number of requests that do not show up in the logs:
- User or device authentications
- Edits to any personal user account, including password resets
- Device commands or state reports, whether by REST or MQTT
- Creation or deletion of Losant events, or the editing of any event
- State retrieval queries, including those made by Losant dashboards
- GET requests (data retrieval) on any organization-owned resource or sub-resource
- Many "pre-process" errors, such as malformed requests, 404s and timeouts
Was this page helpful?
Still looking for help? You can also search the Losant Forums or submit your question there.